On-premises Integration Model
The on-premises integration model is designed for clients who do not want data or traffic to leave their network, who must comply with legislation or regulatory requirements in their country of operation or industry.
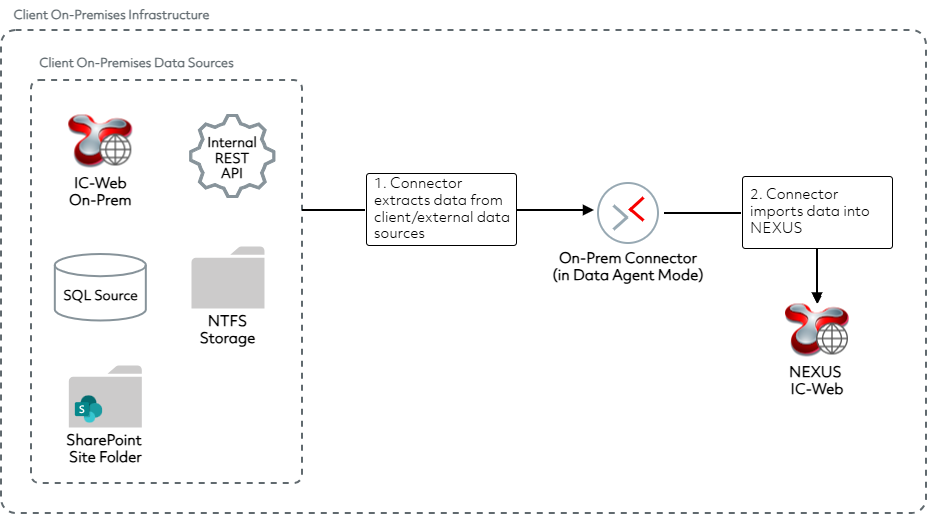
In this model, connectors run within the client’s infrastructure and transfer data into the client’s NEXUS instance using the NEXUS IC-Web interface.
Connector Behaviour
Typically, a Windows-based service application is installed on the client’s infrastructure and runs at intervals agreed with the client. More than one connector can be installed for a client, allowing multiple workflows to obtain data and process it into the NEXUS IC-Web interface from within the client’s infrastructure.
Deployment Topology
Client-hosted infrastructure
This topology is used when the client requires all connectors to be locally installed within their own network. The connectors run as Windows services on a schedule, moving data from various source systems that the client has access to and processing that data into the client’s NEXUS instance via the IC-Web interface.
The following diagram shows an example of a typical setup:
Execution flow
The connector establishes a connection to the on-premises data source and retrieves the required data into the execution flow configured for that connector. Sources driven by dynamic configuration files include:
External REST APIs, connection made over REST with support for OAuth.
Local NEXUS IC-Web, connection made over REST using IC-Web protocols.
NTFS JSON files, connection made to local file systems where JSON files are dropped for processing.
SharePoint site folders, connection made to process JSON files.
SQL sources, connection made over Open Database Connectivity (ODBC), supporting Microsoft SQL Server and Oracle data sources.
The connector then connects to the client’s in-client-infrastructure NEXUS instance via the IC-Web interface and submits the data to NEXUS.
Security Considerations
All REST API traffic between connectors and data sources is:
Encrypted over HTTPS using TLS, with a minimum cipher suite of TLS_RSA_WITH_AES_128_CBC_SHA.
Requires a credential artefact known as a function key, which supports immediate value rotations at a clients’ request.
All inbound and outbound traffic involving on-premises connectors in a hybrid-cloud configuration follows the same security controls described above.