Asset Security¶
Asset security is a feature that allows even more granular control of access to information than our generic Security Permissions table does. It allows you to set what assets in your database you want each user to have access to.
Asset security works on the principle that all users have access to everything by default, and then database admins remove access as necessary. Restricting access is as simple as creating an asset view that contains the parts of the hierarchy to be restricted, and then setting appropriate access rules on that asset view. Parts of the hierarchy can appear in multiple views with multiple security rules — the rules will be applied across all of their views.
Example:
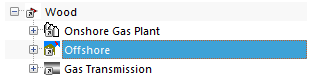
Suppose you have the following asset hierarchy:
If you wish to restrict access to the “Offshore” part of the hierarchy by making it visible to Offshore Engineers but block access to Onshore Engineers, you would:
Log in as an administrator account.
Create a new Asset View — give it a helpful name like “Offshore assets - Offshore Engineers only”.
Display the new Asset View by clicking .
Add a link to the Offshore part of the hierarchy by clicking
- .
- Select the Offshore asset and click OK.
Set the permissions on this asset view by clicking
.
Now set appropriate permissions for each user group:
- For Offshore Engineers: set to Read/Write to give them full access.
- For Onshore Engineers: set to Deny All to block these users.
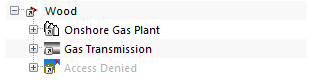
Now, the Offshore Engineers will have full access to that part of the tree, and Onshore Engineers will have no access. This access will be applied across asset views, so that Onshore Engineers will not be able to circumvent their restrictions by switching to a different asset view. If people who are blocked from assets try to view them, they will see:
In setting up asset level security rules, it is important to note that a user will have the lowest access they have set up.
Common gotchas are:
- Removing a user group’s access from the “Default View” — this gives them no access to any assets (as they now have deny access on all assets).
- Where a user belongs to multiple user groups, and one of the groups has access in one view but another group does not have access — the user will not have access to the assets. The rule is that the most restrictive permission is what’s applied.
- Giving a user Read Only access is the same as Deny Write (in this context).
Asset security also applies to Library items. If a library item is connected to an asset that the user has no permission to read and/or write, then the user will similarly have no permission to view and/or edit that library item.
Note that asset security is likely to have an impact on performance, because NEXUS IC must look up every asset to check its security before it can be displayed to the user.